Emerging Technology Trends: Practical Insights for Everyday Users
Outline:
– Why emerging technology matters now for everyday decisions
– Practical AI for real tasks, not just headlines
– Faster connections and edge computing for smoother experiences
– Privacy and security habits that scale without stress
– Cloud, no‑code, and an action plan for next steps
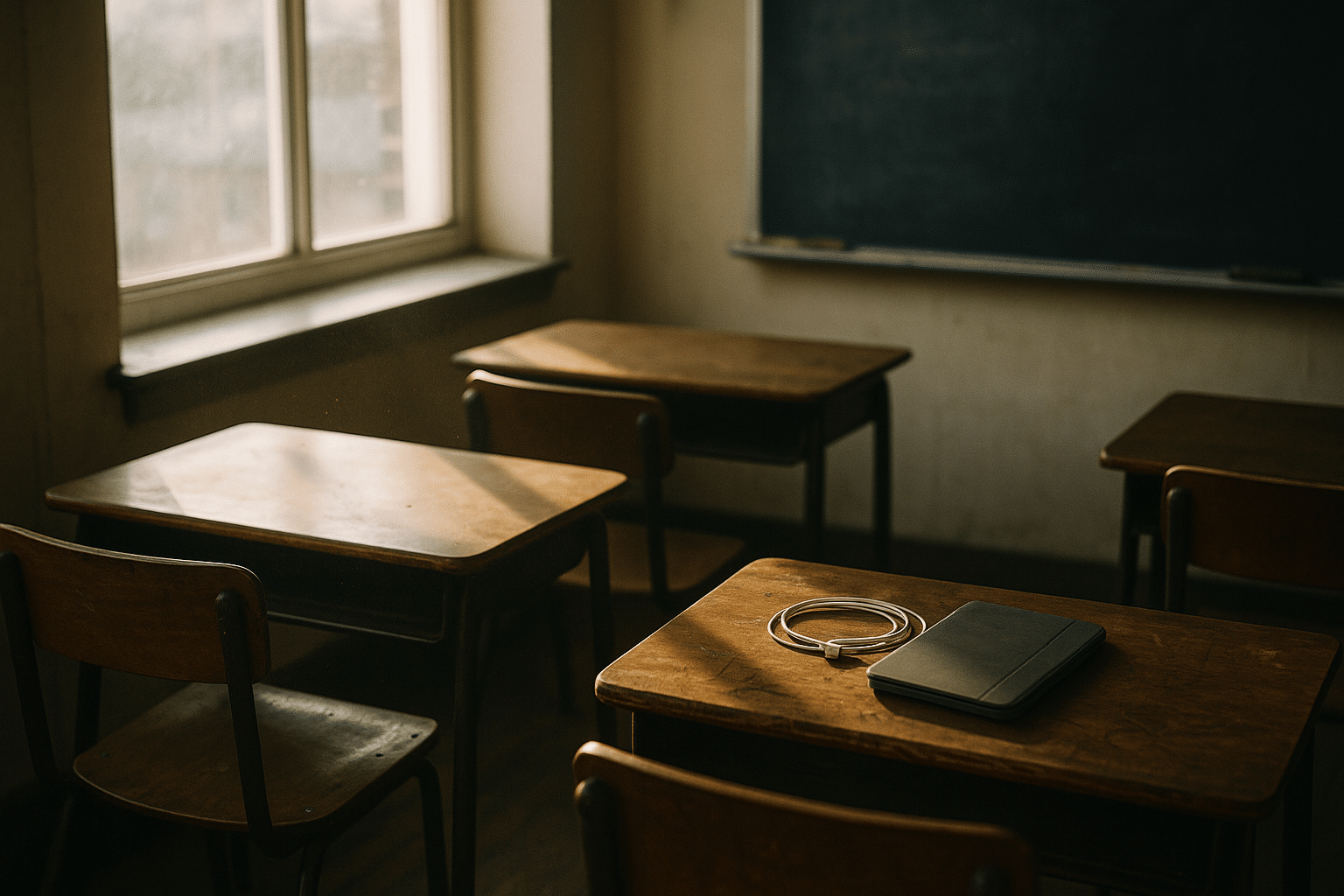
Why These Trends Matter Right Now
Emerging technology is often introduced like a dazzling stage show, but its real meaning appears in quiet moments: a quicker checkout on your phone, a sharper photo in low light, a more stable video call with your family, or a reminder that prevents a missed payment. The signal beneath the noise is simple—when tools save time, reduce errors, and cut effort, they matter. More than two thirds of the planet now connects to the internet, and the average person touches dozens of online services in a week. That’s why understanding the direction of change—rather than every technical detail—has become a practical life skill.
Consider two lenses for judging any trend. First, personal relevance: will this save you five minutes each day, spare you a headache, or help you make a clearer decision? Second, trade‑offs: does it cost money, battery life, privacy, or attention, and is that cost worth the payoff? When framed like this, buzzwords turn into line items on your mental checklist. For example, small on‑device artificial intelligence can translate text offline with low latency, while cloud‑based models handle larger tasks but may use more data. Similarly, newer wireless standards can deliver steadier streaming and faster downloads, but older routers might bottleneck the gains.
Scale also creates new expectations. Homes now host smart sensors, media boxes, and a maze of chargers; workplaces rely on cloud dashboards, video meetings, and automated workflows. With so many moving parts, reliability becomes a first‑class feature. A sluggish connection or a clumsy login ritual can waste hours over a month. That’s why trends like edge computing (processing closer to where data is created) and passkey sign‑ins (streamlined authentication) are drawing attention: they aim to remove friction where it hurts the most—startup time, latency, and cognitive load.
As you read on, treat this guide like a trail map: short markers for each fork in the road, practical notes about terrain, and a few scenic detours for context. The goal isn’t to chase every novelty; it’s to calmly pick the few changes that will compound into a smoother digital routine.
Practical AI You Can Actually Use
Artificial intelligence can feel abstract, yet its most helpful forms are strikingly ordinary. Think of quick language rewrites that tidy an email without changing your voice, summarizers that condense long pages into a few clear points, or camera enhancements that balance tricky lighting on the fly. What makes these features useful is not spectacle but workflow fit: low‑friction assistance that disappears into your habits. Two broad approaches deliver this help. On‑device models are compact and fast, ideal for private, low‑latency tasks like text cleanup or offline translation. Cloud‑based models are larger and more capable, handling multi‑step reasoning, complex drafts, or cross‑document synthesis.
Each path has trade‑offs. On‑device workloads reduce round‑trip time and keep more data local, but they may struggle with nuanced or highly specialized prompts. Cloud systems can be more fluent and wide‑ranging, yet they depend on connectivity and may use more energy on the backend per request. A practical way to decide is to match task heft to model scale: quick, repetitive edits go local; research and long‑form planning go remote. Keep a mental note that AI output is probabilistic. Even strong systems can invent details or misread context, which is why human review matters—especially for names, numbers, dates, and instructions.
Here’s how to turn AI from novelty into quiet utility:
• Draft with intent: outline your point in one or two sentences, then ask for a rewrite by tone (friendly, neutral, formal) and length (concise, two paragraphs).
• Compare options: request side‑by‑side pros and cons with bullet points and a short verdict tied to your constraints (budget, time, offline use).
• Summarize responsibly: for long articles, ask for key claims, evidence, and caveats; verify any quantitative claims you plan to reuse.
• Protect context: avoid pasting sensitive data; when needed, anonymize details or work offline with smaller models.
When evaluating AI features built into apps, look for controls rather than hype. Can you toggle processing between local and cloud? Is there a visible history you can clear? Are there transparent notes on data retention? Features that foreground consent and give you knobs to turn are typically more sustainable. In short, use AI as an amplifier for your judgment, not a replacement for it. The greatest gains appear not in one flashy task, but in dozens of tiny improvements that shave seconds and preserve focus.
Connectivity and the New Edge: Faster, Closer, Smoother
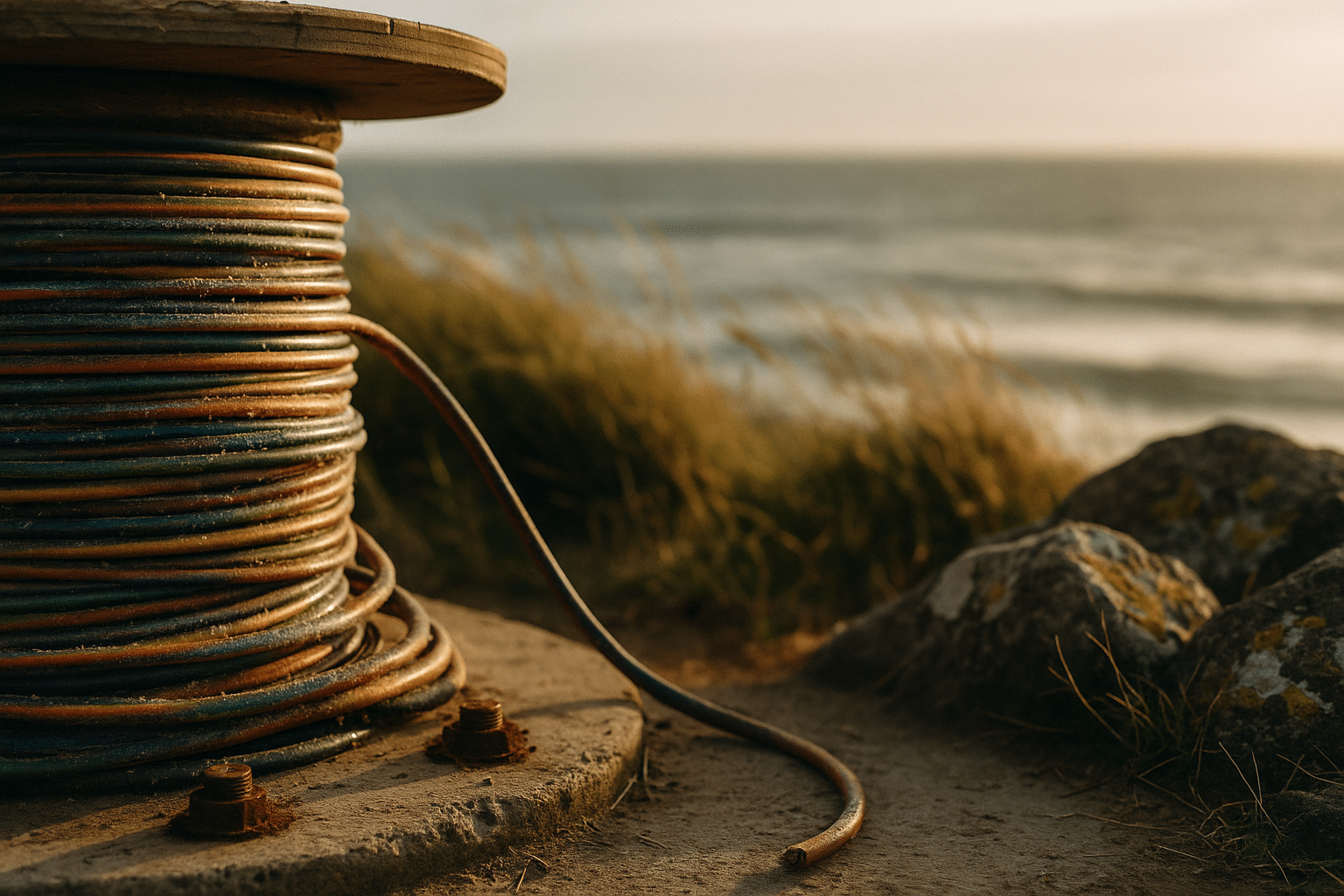
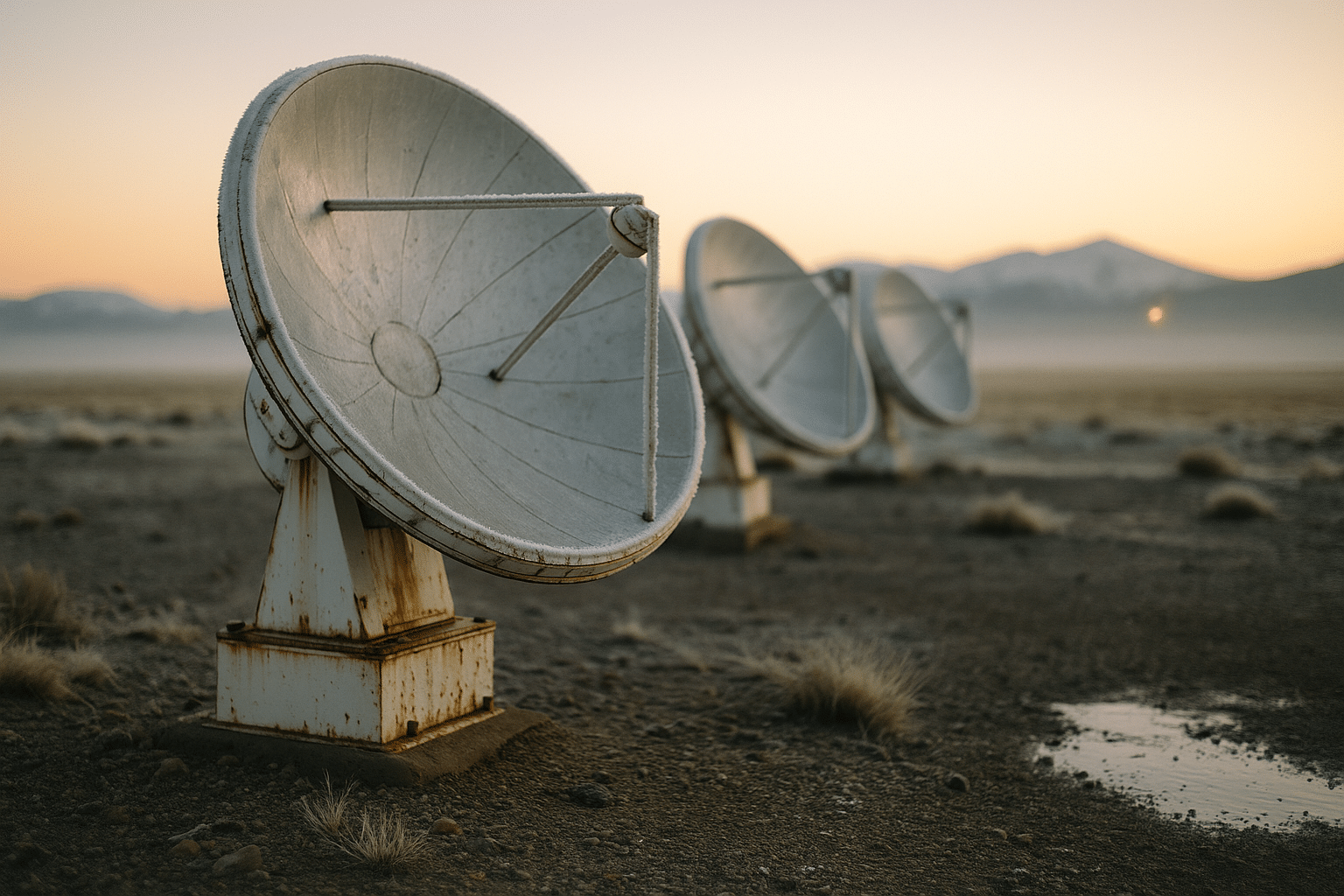
Speed used to be the headline, but consistency is the character you actually live with. Fifth‑generation mobile networks can deliver rapid downloads and lower latency than prior generations, yet real‑world experience depends on coverage, congestion, and the device you hold. At home, newer wireless standards operating on less crowded spectrum can feel like widening a hallway; streams stop stuttering, large files stop crawling. Fiber connections offer sturdy upload speeds for backups and calls, while fixed wireless and modern satellite services have grown into credible options for regions where cables lag.
Edge computing reshapes how that connectivity feels. Instead of sending every task to a distant data center, more work happens near you—on your device, on a home hub, or on a neighborhood node. That closeness trims delay for things like gaming, telepresence, home automation, and real‑time analytics from sensors. It also reduces backhaul traffic, which can lower costs for providers and, over time, help make networks more efficient. For you, the practical test is simple: does the thing you tap respond within a heartbeat? If yes, edge is quietly doing its job.
Choosing the right connection is less about acronyms and more about fit:
• Apartment dwellers: prioritize stable upload speeds and a modern router; walls and neighbors matter more than theoretical peak rates.
• Suburban homes: consider wired backhaul for mesh nodes to avoid wireless bottlenecks; place nodes high and central for coverage.
• Rural users: compare fixed wireless and satellite latency for your address; line‑of‑sight and elevation can be worth a site visit.
• Mobile workers: carry a secondary connection plan for travel days; even a modest backup can save a meeting or deadline.
Small upgrades compound. An affordable Ethernet cable to a streaming box can tame buffering; a router placed off the floor reduces dead zones; a powerline adapter might rescue a distant room. And don’t forget upstream dependencies: if your laptop’s wireless card is old, a sleek new router can’t unlock its potential. Treat connectivity as a chain where the slowest link sets the pace; strengthen links one by one, starting where you feel the pain.
Privacy and Security Habits That Scale
Strong safety isn’t theatrical; it’s routine. Most incidents trace to familiar culprits: weak or reused passwords, phishing lures, unpatched software, and exposed data in places no one remembered. The antidote is small, layered, and boring—in the very best way. Start with authentication. Passphrases beat short passwords, password managers remove the burden of memory, and multi‑factor prompts block the bulk of takeover attempts. Newer passkey systems replace secrets you type with cryptographic keys bound to your device, trimming both friction and risk.
Next, manage surface area. Fewer installed apps mean fewer potential vulnerabilities. Prune browser extensions; many have broad permissions and mixed update histories. Keep operating systems and firmware updated; automatic schedules are your friend. For networks, change the default admin credentials on your router and disable remote management unless you truly need it. Segment curious gadgets (cameras, smart plugs, hobby boards) onto a guest network so a flaw in one place doesn’t wander everywhere.
Phishing remains the most common mess. Messages that create urgency—“verify now,” “unusual activity,” “shipment problem”—deserve extra suspicion. Hover over links, confirm senders, and when in doubt, visit a known site directly rather than tapping a message link. Remember that attackers copy visual styles convincingly; it’s the domain, not the logo, that gives the game away. Data‑wise, collect less and expire more. Turn off background app permissions you don’t use, clear location history periodically, and back up only what you care to keep.
Build your own lightweight playbook:
• One manager for secrets, one authenticator app, and a short list of recovery codes printed and stored safely.
• Monthly five‑minute check: review recent logins, revoke stale tokens, and remove one app or extension you no longer need.
• Quarterly cleanup: export critical data, test restores, rotate high‑value credentials, and verify recovery contacts.
• Annual reset: refresh devices that no longer receive updates; donate or recycle securely after a factory wipe.
You’ll never eliminate risk, but you can corral it. The goal is resilience: a suspicious click becomes an inconvenience, not a catastrophe; a lost phone becomes a replaceable object, not a doorway.
Cloud, No‑Code, and What to Do Next
Cloud services and no‑code tools have turned solo users and tiny teams into nimble operators. Storage that syncs across devices, forms that feed sheets, and visual builders that automate repetitive chores can shave hours from a week. The appeal is clear: lower upfront cost than custom development, quick iteration, and a library of connectors that glue everyday apps together. Yet the quiet details matter. Data portability determines whether you can leave later; rate limits control how fast tasks run; and pricing tiers can make a modest workflow affordable or surprisingly costly depending on triggers and runs.
Think in layers. Start with a single source of truth for tasks and notes, then let automations mirror information outward as needed. For example, a form submission can create a task, send an acknowledgment, and file an attachment into a dated folder, all without supervision. The key is to automate outcomes, not steps: describe the finish line, and then design the fewest reliable actions that reach it. When a tool offers both “simple mode” and “advanced mode,” begin simple and only escalate when you hit a real limit—complexity is a tax you pay forever.
Pragmatic comparisons help keep choices grounded:
• Templates vs. scratch: templates speed success but can hide assumptions; building from scratch is slower but clarifies structure.
• Visual builders vs. scripts: visual tools invite collaboration; lightweight scripts offer precision and version control.
• One suite vs. mix‑and‑match: a single vendor reduces context switching; a mix improves flexibility and reduces lock‑in risk.
• Local vs. cloud: local tools offer privacy and offline reliability; cloud tools offer reach, collaboration, and elastic capacity.
Here’s a simple action plan to close the loop on this entire guide:
• Pick one micro‑win this week: an AI rewrite for routine messages, or a summarizer for long reads.
• Fix one network link: reposition your router or add a wired backhaul to a busy room.
• Lock one door: enable multi‑factor for a high‑value account and prune two unused app permissions.
• Automate one chore: move attachments to a dated folder with a clearly named rule.
Small, compound steps beat sweeping overhauls. By choosing a handful of upgrades that fit your life—faster, closer compute where latency hurts; AI where repetition drags; guardrails where risk concentrates—you’ll feel the difference in calmer mornings and fewer digital detours. Technology becomes the quiet helper it’s meant to be, not another tab to manage.